in February 2016, the experts “Kaspersky Lab” presented a report on the family malware Acecard, calling these mobile banking Trojans one of the most dangerous threats in the present.
Now your report Troyan Acecard published and the researchers of McAfee. A new version malware. If earlier Acecard spread, in particular, and through the official Google Play Store, masquerading as card apps and games, now operators malware changed tactics.
New Acecard distributed via third-party directories and pretends to be Adobe Flash Player, pornographic apps or codecs. Once on the device, this app starts to plague the user with repeated requests, and does not stop until, until you get what you want administrator privileges. After that, malware for some time silent and waits for the user to launch a particular application. So, McAfee detected a Trojan, waiting for the launch of Google Play, and then resorted to social engineering.
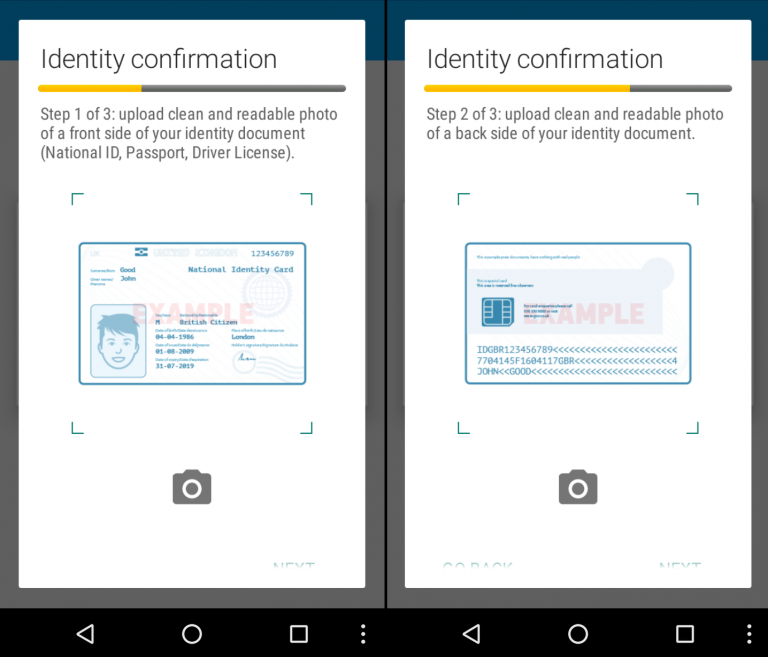
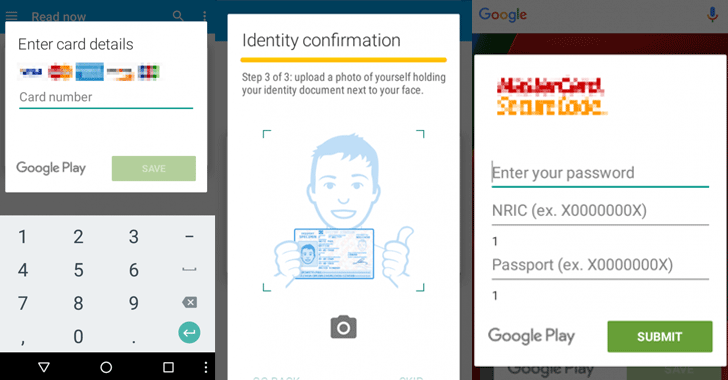
Initially, the Trojan displays on top of the application window its own and asks the user to enter a credit card number. Then, other pop-up Windows, Acecard requests other information about the card, for example, date of expiry, and asks the victim to provide information proving the identity. Studied by experts McAfee version of the Trojan is aimed mainly at users from Hong Kong and Singapore, so malware interested in local documents. If the user has fulfilled all the requests of the Trojan, Acecard goes to the final step and asks the victim to take a selfie while holding in the hands of the ID.
“It can be very useful for cybercriminals, as they will be able to confirm the victim’s identity and get access not only to her Bank account, but perhaps even accounts in social networks,” write the researchers.
a self, along with other information, can indeed be used to confirm banking transactions, or contacting the support of social networks and other services.
Analysts say that this version of the Acecard is not only interested in Google Play. With the help of fake Windows malware also collects credentials from other apps including Facebook, WhatsApp, WeChat, Line, Viber, Dropbox, Google Music, Google Books and Google Videos.
No comments:
Post a Comment